
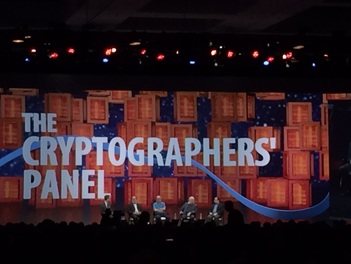
 RSA 2104 - the Cryptographers' panel: First two of the three RSA "letters" were here -- Ron Rivest and Adi Shamir -- and Whitfield Diffie. Shamir said that cryptography is not a problem of modern security. There are no breaches associated with the cryptographic algorithms. It's algorithm applications, or implementations that fails. The PCI SSC meeting (1400 participants) is over. Mostly, minor clarifications in PCI DSS and PA-DSS 3.0, changes in PTS testing requirements 4.0. Unfortunately, no significant changes in PCI standards means no good news for merchants and cardholders. No regulation or tech breakthroughs means the show will go on.
PCI SSC has released a document that "highlights anticipated changes to the PCI Data Security Standard (PCI DSS) and Payment Application-Data Security Standard (PA-DSS) in order to prepare organizations for the introduction of Version 3.0 in November 2013".
I could not find any significant changes that would help to improve the security of card payment transactions. I wasn't surprised though. I just found a list of "PCI myths" on some website about PCI compliance. One of the myths sounds familiar and reasonable, although the explanation (they call it "fact") sounds polite but unconvincing and incomplete: Myth: PCI will make us secure. Fact: Successful completion of a system scan or assessment for PCI is but a snapshot in time. Security exploits are non-stop and get stronger every day, which is why PCI compliance efforts must be a continuous process of assessment and remediation to ensure safety of cardholder data. Finally, Twitter has implemented 2-factor authentication of their accounts. It is made possible with SMS messages. When you log in to your twitter account, in addition to username and password, you will be prompted for 6-digit code which is sent to your mobile phone. Similar technology is used by some other companies (for example, Facebook and Bank of America). This is not the best solution (what if you are located in out of service zone?) but it is better than nothing. There are more robust solutions, which also use mobile phone, implemented, for example, by Google or PayPal. They utilize software tokens: different smartphone apps (Google Authenticator and VeriSign VIP accordingly) that, however, do the same: display new temporary code every minute. Such app generates the numbers based on preset initialization vector and mathematical formula, which does not require any server connection. Therefore, the phone device with such app can be used offline, the same way as classic hardware token like RSA SecurID.
I have been comparing several Track/PAN detection tools and this one looks pretty good. Later on I am going to publish a comparison chart of several such products (both commercial and free). If you have any comments/links please let me know.
One more incident with fake website certificates: Turkish Certificate Authority screwup leads to attempted Google impersonation.
The fake certificate was issued by Turkish certificate authority - TurkTrust: After reporting the incident, TURKTRUST discovered it had accidentally issued two intermediate certificates instead of normal site certificates in August 2011, including the one used to sign the fake Google certificate. There is a new Mastercard which has LCD screen and keyboard. It looks like the plastic becomes smarter and closer to POS terminal in its functionality which I guess will bring new security issues...
There is a new password protection technology available from RSA. They split the passwords in two and store them on two separate servers in two different locations so if one server/location is compromised it does not compromise the whole password. This is interesting idea, but what about performance, and what if both servers are compromised (probably, they are going to be managed by the same entity)?
|
Books
 Crypto Basics Crypto Basics
 Bitcoin for Nonmathematicians: Exploring the Foundations of Crypto Payments Bitcoin for Nonmathematicians: Exploring the Foundations of Crypto Payments
 Hacking Point of Sale: Payment Application Secrets, Threats, and Solutions Hacking Point of Sale: Payment Application Secrets, Threats, and Solutions
Recent Posts
Categories
All
Archives
March 2023
|




 RSS Feed
RSS Feed
