|
My new book Bitcoin for Nonmathematicians is now available in Amazon Kindle and B&N Nook ebook formats
0 Comments
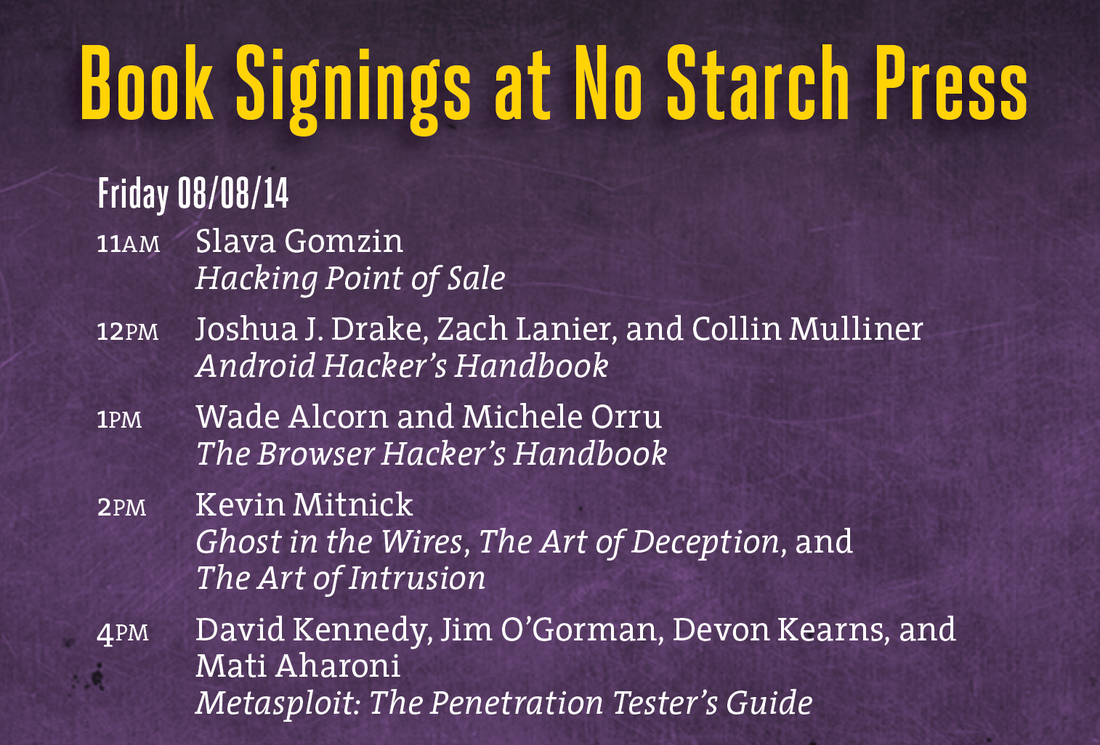
I'll be doing two one-hour book signings at Black Hat USA 2014 and DEF CON 22 conferences in Las Vegas: Black Hat USA 2014: August 6, 2014, 5:30 pm Mandalay Bay Conference Center, Tripwire booth 141 (I'll be doing a short presentation before the book signing) DEF CON 22: August 8, 2014, 11:00 am Rio Hotel & Casino, No Starch Press community table in Vendor Area If you have free access to government or university supercomputer - don't miss your chance to become a millionaire! the National Science Foundation (NSF) revealed that more than $8,000 (£4,760) worth of bitcoins had been generated from NSF-funded computers. A member of the Harvard community was stripped of his or her access to the University’s research computing facilities last week after setting up a “dogecoin” mining operation using a Harvard research network. Bitcoin exchange Vircurex stops withdrawals due to "two incidents last year that lead to a loss of a significant number of BTC, LTC, FTC, TRC". Frozen Funds Bitcoin developers released the new version of client software which includes the fixes for transaction malleability bug. This bug enabled attacks on Bitcoin exchanges. Transaction malleability-related fixes This is second shutdown event of Bitcoin service provider after recent online exchange Mt. Gox bankruptcy caused by the flaw in Bitcoin transaction processing design. According to the message on Flexcoin website, they are closing their business but still going to publish the details of the attack as soon as they are available. There are several interesting observations that I made based on recent Bitcoin events (I mean recent attacks on Bitcoin exchanges and Silk Road 2). First of all, I did not know until yesterday that there is Silk Road 2! Very little time has passed since the disappearance of Silk Road 1. That was fast! Second, now I can create a new category called "Bitcoin Breaches" so the existing Card Data Breaches section can relax a bit (it's overloaded and worked too hard since December last year) . And finally, it turns out that the bug, which caused all recent Bitcoin breaches, is not new, and the attack vector was described almost 3 years ago! The following post is dated May 15, 2011. So you can sit on the network, watch for transactions, and echo them with the signatures slightly tweeked, but still valid. These new transactions will have different hashes, and will compete with the original transactions for inclusion in a block. When a cloned transaction beats out the original for block inclusion, it will leave the original in the owners wallet unconfirmable forever, resulting in inconvenience and unspendable coins. Quick echoing and network latency gives this a finite chance of happening. You can also find a decent explanation, which (hopefully) does not require a deep technical understanding of the Bitcoin implementation, of transaction malleability (that's how this bug was eventually named - beautiful name!) here. |
Books
 Crypto Basics Crypto Basics
 Bitcoin for Nonmathematicians: Exploring the Foundations of Crypto Payments Bitcoin for Nonmathematicians: Exploring the Foundations of Crypto Payments
 Hacking Point of Sale: Payment Application Secrets, Threats, and Solutions Hacking Point of Sale: Payment Application Secrets, Threats, and Solutions
Recent Posts
Categories
All
Archives
March 2023
|
Slava Gomzin




 RSS Feed
RSS Feed
